This article contains affiliate links. We may earn a small commission when you purchase through these links, at no additional cost to you. This helps us keep ThinkEV running.
⚡ Key Takeaways
- ✓Mozilla's Privacy Not Included project found that 84% of car brands reviewed collected more data than necessary.
- ✓The exposed data included precise GPS locations for 460,000 of those vehicles, linked to customer identity information.
- ✓The fine was small ($175,000 USD), but the enforcement action occurred.
- ✓Compare this to the GDPR's potential fines of up to 4% of global annual revenue.
Let me tell you what's actually happening with Chinese EV cybersecurity — because most of what you've heard from politicians and pundits is incomplete, misleading, or driven by trade policy rather than technical reality.
I've spent the last several months digging through privacy policies, academic research, government advisories, and regulatory filings. I talked to security researchers. I read the actual Transport Canada documentation. I looked at what data Tesla, BYD, Hyundai, GM, and Volkswagen actually collect — not what their PR departments say they collect, but what's documented in their privacy policies, what's been discovered by independent auditors, and what's been exposed in data breaches.
Here's my conclusion: Chinese EVs present data privacy risks that are real but frequently overstated. Western EVs — including Tesla, GM, and Volkswagen — present data privacy risks that are equally real and almost never discussed with the same urgency.
If you're worried about your connected car collecting data and transmitting it to a government that shouldn't have it, you should be worried about every connected car on the road today. Starting specifically with Chinese brands because of a geopolitical frame is understandable. It's just not actually well-calibrated to the risk.
That said — the risks are not zero. There are legitimate concerns about Chinese EVs that deserve serious examination. There are things you should know before you buy. And there are gaps in Canada's privacy law that leave every EV owner — regardless of brand — poorly protected.
That's what this piece is about. Not panic. Not dismissal. The actual picture.
🔐 Key Findings
- ◆ Tesla collects significantly more granular data than any Chinese EV currently sold or planned for Canada — including external camera footage and cabin audio sampling
- ◆ There are zero confirmed, documented cases of BYD or any Chinese EV brand transmitting Canadian user data to the Chinese government
- ◆ The VW Group exposed 800,000 customer records — including precise GPS locations — in December 2024. Western brands, not Chinese ones.
- ◆ Canada's PIPEDA is inadequate for the connected car era. There is no vehicle-specific data standard equivalent to the EU's WP.29 regulation
- ◆ China's 2021 National Security Law creates a legal obligation for Chinese companies to cooperate with intelligence requests — a structural risk that is different in nature from Western data brokers selling your data commercially
- ◆ The real gap is regulatory: every Canadian EV owner has weaker protections than their German or Australian counterpart, regardless of which brand they drive
The Political Frame vs.
The Technical Reality
Before we get into the data, we need to acknowledge that this conversation is almost impossible to have cleanly because it lives at the intersection of national security concerns, trade policy, and consumer privacy law — three domains with very different incentive structures and very different definitions of "risk."
The political frame looks like this: China is a strategic adversary. Chinese companies are legally required to cooperate with Chinese intelligence requests under the 2017 National Intelligence Law and 2021 Data Security Law. Therefore, Chinese EVs could be intelligence-gathering tools. Therefore, we should restrict or ban them.
This argument has real substance. The legal structure in China is genuinely different from what exists in liberal democracies. The National Intelligence Law is not hypothetical — Article 7 explicitly requires organizations and citizens to "support, assist, and cooperate with the state intelligence work." A Chinese EV maker cannot legally refuse a data request from Chinese state security services, even if that data was collected from Canadian customers.
That's a fact, not a paranoid fantasy.
But here's where the political frame oversimplifies: it assumes this legal risk is unique to Chinese companies, that Chinese EVs collect data in uniquely dangerous ways, and that Western governments and companies are structurally safer. None of those assumptions are cleanly true.
The US has FISA Section 702, which permits warrantless collection of foreign nationals' data held by US companies. American tech companies — which power a large fraction of connected car infotainment through Google Android Automotive and Apple CarPlay — regularly comply with government data requests. GM's OnStar was caught selling driver behaviour data to insurance companies without explicit customer consent in 2023. Mozilla's Privacy Not Included project found that 84% of car brands reviewed collected more data than necessary.
The structural risk from Chinese companies is real and distinct. But it doesn't exist in a vacuum where Western alternatives are clean.
With that framing established — let's look at what the data actually shows.
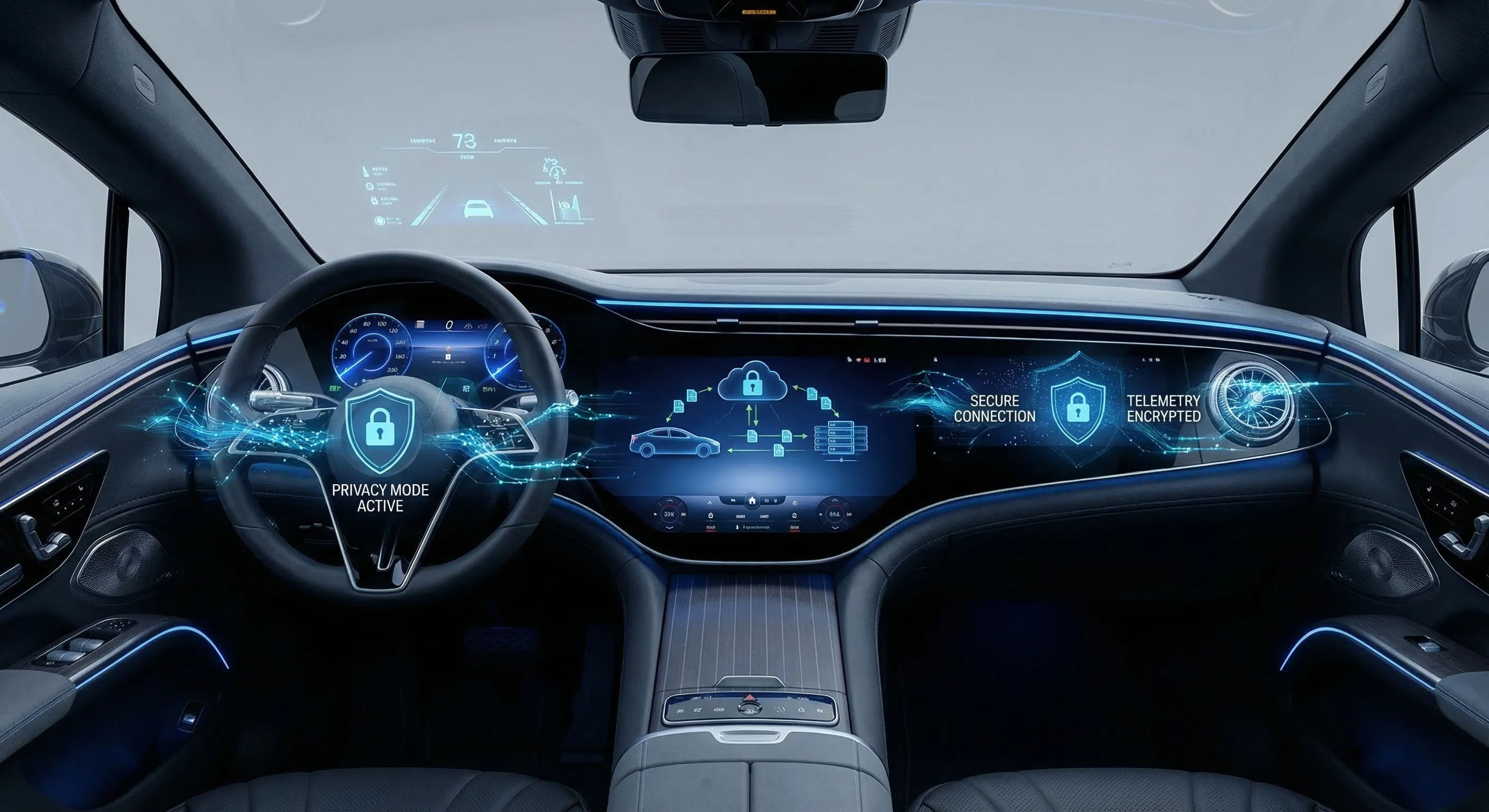
What Modern EVs Actually Collect
The connected car has become, quietly, one of the most invasive consumer data collection platforms ever built. It's in the same league as your smartphone — except most people haven't thought through the privacy implications the way they at least nominally have with phones.
Here's what a modern connected EV typically collects:
Location data. This is universal. Every connected EV with a navigation system or remote monitoring app records your location history. Not just your current position — your full movement history: where you live, where you work, what medical appointments you attend, what political meetings you go to, which religious institutions you visit. A complete picture of your physical life, timestamped and stored on remote servers.
Driving behaviour. Speed, acceleration, braking, steering inputs, energy consumption. For insurance-priced EV programs, this data feeds directly into rate calculations. For manufacturers, it feeds into product development and over-the-air update targeting.
Vehicle health telemetry. Battery state of health, motor temperatures, software versions, error codes. This is largely benign — it's what makes remote diagnostics possible and what enables over-the-air software fixes. But it represents a continuous data stream from your car to manufacturer servers.
Infotainment data. This is where things get uncomfortable. Many EVs sync contacts, calendar events, and call logs from connected phones. Some record preferred radio stations, podcast history, and app usage. Depending on the vehicle and whether you've enabled voice assistants, snippets of in-car audio may be sampled.
Cabin and external cameras. Tesla is the most aggressive here. Sentry Mode records external camera footage continuously when the car is parked. Tesla has acknowledged using this footage — and footage from inside the cabin — for product development purposes. Other brands have varying degrees of camera capability; most are more restrained than Tesla.
VIOFO A229 Pro 4K Dash Cam
4K front + 2K rear with parking mode and GPS. Your silent witness for insurance claims. Hardwire it for always-on sentry recording while your EV is parked.
We may earn a commission at no extra cost to you.
Biometric data. This is currently limited but expanding. Driver monitoring systems track head position and eye movement for fatigue detection. Some Chinese EVs (particularly higher-end NIO models) have used facial recognition for driver profile customization. This data category is the one I'd watch most carefully as the technology matures.
The scale of this collection is hard to internalize until you see it enumerated. McKinsey estimated in a 2021 report that a connected vehicle generates approximately 25 gigabytes of data per hour of operation. That's more data per hour than most households generate in a week. And almost none of it is subject to meaningful consumer control.
Who Actually Collects the Most?
If you rank EV brands by data collection aggressiveness — based on published privacy policies, independent audits, and what's been documented in security research — Tesla is consistently at or near the top.
Tesla's privacy policy permits collection of:
- "information about your vehicle and how it is used, including your vehicle's battery level, speed, braking, swerving, and acceleration"
- "in-car communications such as phone calls, text messages, voicemails, and audio recordings"
- "footage from the camera system (including footage related to auto pilot and safety events)"
- contacts, calendar entries, and location history
Tesla explicitly notes it "may collect, use, and transfer Personal Information as required or permitted by applicable law, including transferring data out of your country of residence to the United States." Your data goes to US servers, under US law, accessible to US government agencies with FISA warrants.
I want to be clear: I'm not arguing Tesla is more dangerous than BYD. I'm arguing that the data collection practices of the world's most-discussed "safe" EV brand should calibrate your baseline before you evaluate Chinese brands.
BYD's published privacy documentation for international markets states that personal data collected in a given country is stored on servers in that country or in countries with adequate data protection agreements. Their Europe-market privacy policy is GDPR-compliant. Their Australia-market policy complies with the Australian Privacy Act.
What BYD's policy does not clearly state — and this is a legitimate criticism — is what happens to data when the car is connected to Chinese-market servers during software updates, or what BYD's obligations are under Chinese law if state security services request data from their servers.
That ambiguity is the real risk. Not that BYD is definitely transmitting your data to the PRC. But that the structural legal conditions for that transmission to happen legally exist, and BYD's public documentation doesn't clearly address what safeguards prevent it.
The Chinese National Security Law Problem

This is the part of the conversation that deserves the most careful treatment, because it involves real geopolitical risks dressed up in technical language.
China's 2017 National Intelligence Law, 2021 Data Security Law, and 2021 Personal Information Protection Law create a layered legal framework that has no clean analog in democratic countries. The core issue:
Article 7 of the National Intelligence Law states: "Any organization or citizen shall support, assist, and cooperate with state intelligence work in accordance with law." The word "shall" is not permissive — it's mandatory.
The Data Security Law requires Chinese organizations to "provide assistance and support" to national intelligence or security authorities. This applies to Chinese companies operating in China.
Here is the critical question for Canadian BYD buyers: does this apply to data stored outside China?
The honest answer is: it's legally ambiguous, practically uncertain, and politically contested.
The Chinese government's position is that Chinese companies must comply with Chinese law, including intelligence requests, regardless of where data is stored — similar to how the US Cloud Act asserts US jurisdiction over data held by US companies on foreign servers.
BYD and other Chinese manufacturers operating in Western markets argue — credibly — that they compartmentalize data by jurisdiction, store local market data locally, and that cross-border data requests would violate the laws of the destination countries (GDPR in Europe, PIPEDA in Canada).
Security researchers and national security agencies take a more cautious view: the legal obligation exists in Chinese law, Chinese companies cannot legally refuse such requests, and there is no effective mechanism for a foreign government to verify whether compliance is occurring.
The Australian Strategic Policy Institute, the UK National Cyber Security Centre, and the US Cybersecurity and Infrastructure Security Agency have all issued advisories noting this structural risk with Chinese technology companies broadly. None have produced specific evidence of Chinese EVs being used as intelligence collection tools.
The bottom line: the risk from China's legal framework is structural and real. It's different from the risk of a Western brand selling your data to insurance companies — the latter is commercial exploitation of your data, the former is potential state surveillance. Both are bad. They're bad in different ways.
What I would tell a Canadian buyer: this risk is real enough to take seriously, but it should be evaluated proportionally. Your smartphone likely transmits more data of higher intelligence value than your car. Your Google searches, your email, your WhatsApp conversations — all of that goes to American servers under American law with American government access. If you've accepted that risk calculus, the incremental risk from a Chinese EV, relative to the total connected-device picture of your life, is smaller than the political discourse suggests.
If you've decided to minimize Chinese government access to your data broadly, then a Chinese EV is consistent with other choices you'd be making. If you haven't thought about this at the phone/app level, doing so at the car level alone is somewhat inconsistent — though it's still a reasonable place to start.
The Infographic: Data Reality in Canada
What Actually Happened in Recent Cybersecurity Incidents
Let's look at the track record, not the theoretical risk.
The Volkswagen Group Breach — December 2024
In December 2024, a German IT security group discovered that Volkswagen Group's subsidiary Cariad — which handles software and connected car services for VW, Audi, Seat, Škoda, and CUPRA — had left approximately 800,000 customer records exposed in an Amazon cloud storage misconfiguration.
The exposed data included precise GPS locations for 460,000 of those vehicles, linked to customer identity information. Volkswagen Group customers in Germany, Norway, Sweden, the United Kingdom, and the Netherlands were affected. The data was precise enough that researchers could determine that several politicians, police officers, and intelligence service employees were among the affected customers.
This is a Western brand. European servers. GDPR jurisdiction. The data didn't go to the Chinese government — it sat in an exposed Amazon S3 bucket accessible to anyone who knew where to look.
No one called for a ban on Volkswagen EVs as a result. The incident barely registered in North American coverage. It received a fraction of the media attention that hypothetical Chinese EV data risks receive.
The GM OnStar Data Sales — 2023
General Motors' OnStar subsidiary was discovered in 2023 to have been selling detailed driver behaviour data — hard braking events, rapid acceleration, speed above limits — to insurance companies including LexisNexis and Verisk. This data was then used to adjust driver insurance rates, sometimes without the drivers' knowledge.
GM did this without adequate disclosure. A Texas class action lawsuit followed. Several states opened investigations. The FTC issued guidance on connected car data.
GM is a Canadian-market EV seller. The Equinox EV qualifies for the federal EVAP rebate. The Ultium platform is connected. This happened.
Tesla Camera Footage Sharing — 2023
Reuters reported in 2023 that Tesla employees had shared videos and images captured by customers' car cameras between 2019 and 2022, including footage of accidents, road rage incidents, and sensitive situations. At least one incident involved footage of a naked man walking toward a vehicle.
Tesla's privacy policy technically permitted this use — the policy at the time stated that footage could be used for "developing, improving, and supporting Tesla's products and services." But customer awareness of what that actually meant was near zero.
The XPeng Facial Recognition Fine — 2021
XPeng Motors was fined by Chinese authorities in 2021 for collecting facial recognition data in its Shanghai showrooms without adequate disclosure. Notably, this was Chinese authorities fining a Chinese company for privacy violations — against Chinese consumers. The fine was small ($175,000 USD), but the enforcement action occurred.
This example cuts both ways. It shows Chinese companies are subject to domestic privacy enforcement. It also shows the privacy culture in China's EV sector has had real problems. Neither reading is fully satisfying.
The BYD Track Record
BYD has had no major documented data breach or unauthorized data-sharing incident in its international markets as of March 2026. This is a meaningful absence, though it's not the same as a clean bill of health — it could reflect good security practices, or it could reflect the fact that BYD's international market presence is relatively recent and hasn't been subjected to the same volume of independent security auditing as Tesla.
BYD commissioned a third-party security audit for its European market launch, the results of which were reviewed by the German TÜV automotive certification body. No critical vulnerabilities were publicly disclosed from that process.
Canada's Privacy Law: Where the System Is Failing You
Here's the part where I shift from describing the problem to describing what should be done about it — starting with an honest assessment of where Canada's regulatory framework stands.
The Personal Information Protection and Electronic Documents Act (PIPEDA) is Canada's federal private-sector privacy law. It came into force in 2000, was written for a pre-smartphone era, and has been inadequate for connected vehicles since the first one rolled off the line.
PIPEDA operates on consent-based principles. Companies collecting personal information are supposed to get meaningful consent, use data only for the stated purpose, protect it with appropriate security measures, and give individuals access to their own data. These principles are sound. Their application to connected vehicles is deeply inadequate.
Here's why PIPEDA falls short for connected cars:
The consent framework is broken. You cannot meaningfully consent to 25 gigabytes of data generation per hour when you sign a car purchase agreement. The privacy policy is a legal document that no one reads, that's written by lawyers to maximize the company's freedom of action, and that covers data practices most customers don't understand and couldn't evaluate even if they tried. Nominal consent is not meaningful consent.
There's no vehicle-specific standard. The EU's United Nations Regulation No. 155 (WP.29) is a cybersecurity management system requirement that all vehicles sold in EU member states must meet. It requires manufacturers to implement cybersecurity risk management throughout the vehicle lifecycle, including data security. Canada has no equivalent. Any EV manufacturer can enter the Canadian market with their connected car platform and face only general PIPEDA requirements, which were never written with connected vehicles in mind.
Data residency requirements are weak. PIPEDA permits cross-border data transfers without explicit consumer consent, as long as equivalent protection is maintained in the receiving jurisdiction. This creates a paper protection that's difficult to verify and rarely enforced. A Chinese EV manufacturer saying "we maintain PIPEDA-equivalent protection when data is transferred" is not auditable under current Canadian law.
There's no independent enforcement with teeth. The Office of the Privacy Commissioner can investigate, make recommendations, and publish findings. It cannot impose fines. Compare this to the GDPR's potential fines of up to 4% of global annual revenue. The privacy violation penalties in Canada are not a meaningful deterrent for a global manufacturer.
The forthcoming Bill C-27 helps, but is incomplete. Bill C-27 (the Consumer Privacy Protection Act) has been working through Parliament and would replace PIPEDA with a more modern framework. It includes stronger consent requirements, new data portability rights, and administrative monetary penalties up to $25 million or 5% of global revenue. However, as of this writing, it has not received Royal Assent, and it still doesn't include vehicle-specific provisions comparable to WP.29.
Quebec is ahead of the rest of Canada. Law 25 (Act Respecting the Protection of Personal Information in the Private Sector), which came into force in stages through 2023, is significantly more rigorous than PIPEDA. It requires privacy impact assessments for high-risk data uses, has stronger breach notification requirements, and gives the Commission d'accès à l'information real enforcement powers. If you're a privacy-conscious EV buyer in Quebec, you have more legal protection than anywhere else in Canada.
What Canada Should Do
I'm going to be direct here: the Canadian government's response to connected car data risks has been almost entirely focused on trade policy — tariffs and import restrictions — rather than privacy regulation.
Banning or restricting Chinese EVs through tariffs does not solve the data privacy problem for Canadian EV buyers. It just means the privacy violations continue with Western brands, which are documented to be at least as aggressive at data collection. If the concern is actually about privacy and data sovereignty, the policy response should be a strong vehicle data standard that every manufacturer selling cars in Canada must meet — regardless of origin.
That means:
- A mandatory cybersecurity management system requirement for connected vehicles (equivalent to WP.29) as a condition of type approval
- Data minimization requirements: manufacturers should collect only what is technically necessary for vehicle operation and declared service features
- Explicit data residency rules: Canadian customer data must be stored in Canada or in jurisdictions with equivalent privacy laws and verifiable enforcement
- Real enforcement: administrative monetary penalties with actual deterrent effect, not just recommendations
- Right to disconnect: consumers should have a legal right to opt out of non-essential data collection without losing core vehicle functionality
None of this would require banning Chinese EVs. It would require all manufacturers — including Tesla, GM, Hyundai, and VW — to meet the same standard. Chinese manufacturers that meet that standard pose the same regulatory risk as any other brand. Chinese manufacturers that don't meet the standard shouldn't be on Canadian roads, and neither should Western ones that fail.
The National Security Layer: Military Installations and Infrastructure Mapping
The national security concern that deserves the most serious treatment.
The concern from security agencies isn't primarily about individual consumer privacy. It's about aggregate data at a national infrastructure level.
If a fleet of Chinese EVs with high-definition cameras and precision GPS operates across Canada — particularly near military bases, critical infrastructure, government facilities, and border crossings — the aggregate imagery and movement data could, theoretically, be valuable for military intelligence purposes.
This is the argument that led Australia to ban Chinese EVs (specifically certain models) from defence facility parking lots. It's the argument behind US legislative proposals to restrict Chinese EV sales near military installations. It's a structurally different argument from "your personal data will be stolen."
The honest assessment: this concern is more substantive than most individual consumer privacy discussions acknowledge, and less substantive than the most alarmist national security commentary suggests.
Modern commercial satellites already provide high-resolution imagery of Canadian military bases on a regular basis. Google Maps and Apple Maps have detailed street-level imagery of most Canadian infrastructure. Chinese tech companies don't need EVs to do cartographic intelligence gathering — the commercial data already available through normal channels is extensive.
What EVs potentially add is dynamic, real-time, or frequently updated high-resolution imagery with movement data — which could theoretically be more valuable for certain intelligence applications than static satellite imagery.
The UK's response has been proportionate: guidance to avoid parking Chinese EVs at certain sensitive facilities, without a blanket ban. That's probably closer to the right calibration than either complete dismissal or full prohibition.
For the vast majority of Canadian consumers driving in civilian contexts, this concern is not relevant to their personal situation. If you're a military officer stationed at CFB Petawawa, you might want to think twice about a connected Chinese vehicle. If you're driving to work at a call centre in Kelowna, the geopolitical intelligence risk of your BYD is approximately zero.
What Specific Chinese EV Brands Are Doing
Rather than treating "Chinese EVs" as a monolith, let's look at the specific brands most relevant to the Canadian market.
BYD
BYD is the most relevant brand for Canadian buyers right now, given the tariff deal and their Transport Canada type approval.
BYD's data architecture for Western markets uses localized data storage — European customer data is stored on servers in Germany, Australian customer data in Australia. Their international privacy documentation was updated in 2024 to align with GDPR requirements, which are significantly stronger than Canadian PIPEDA requirements.
BYD's vehicles communicate primarily with BYD's own backend infrastructure rather than third-party platforms. Unlike some competitors, BYD has not embedded Google Android Automotive OS or similar third-party platforms with their own independent data collection.
What's less clear: the relationship between BYD's international market data infrastructure and BYD's China-based systems. BYD is a Chinese company subject to Chinese law. Their international data commitments are a function of their contractual and legal obligations in export markets — not a structural separation from Chinese government jurisdiction.
The risk is real but theoretical. There is no documented evidence of BYD providing Canadian customer data to Chinese intelligence services. The structural conditions for it to happen if compelled to do so exist.
NIO
NIO is not yet in the Canadian market, but it's worth examining because it represents a different end of the data collection spectrum among Chinese brands.
NIO's service model is built around NOMI, an AI-powered in-car assistant that requires persistent connectivity and extensive data collection to function. NOMI processes voice commands, learns driver preferences, integrates with NIO's battery swap network, and provides predictive maintenance. This architecture requires substantially more data collection than a more conventionally connected EV.
NIO's privacy documentation for European markets is GDPR-compliant, but the NIO-specific service features require agreeing to considerably more data sharing than base vehicle operation. If you want NOMI to work, you're opting into extensive data collection.
NIO also experienced a significant data breach in December 2022, when a hacker exfiltrated approximately 486MB of user and vehicle data and attempted to extort the company. NIO disclosed the breach and cooperated with Chinese authorities in the investigation. The data was stolen by a criminal actor, not accessed by the Chinese government — but the incident demonstrates that NIO's data infrastructure has been successfully attacked.
XPeng
XPeng's vehicles include advanced driver assistance and autonomous driving features that require similar data collection to Tesla — camera imagery, sensor data, and driving behaviour — to train their systems.
XPeng has had documented incidents with privacy violations in China (the facial recognition fine mentioned earlier) and has faced scrutiny from European regulators as it has expanded into that market. Their GDPR compliance has been reviewed and appears to meet baseline requirements.
XPeng's primary market is China, and their engineering culture reflects that. Their connected systems are more deeply integrated with Chinese infrastructure than BYD's, in my assessment. This would make data segregation between Chinese and international market systems more challenging to implement and verify.
SAIC (MG)
MG, owned by SAIC Motor (Shanghai Automotive Industry Corporation), is already selling vehicles in Canada and is the Chinese brand with the longest Western market presence. MG vehicles generally use conventional connected car architectures without the deep AI-assistant integration of NIO or XPeng.
SAIC is partially state-owned — a controlling interest, with Shanghai municipal government entities holding majority ownership. This makes it structurally different from privately held companies like BYD, though all Chinese companies remain subject to the National Intelligence Law regardless of ownership structure.
MG's UK data privacy practices were reviewed as part of the UK market entry process and were found to be compliant with UK GDPR. The UK is not Canada, but it's a useful reference point — a rigorous independent privacy review found no material violations.
Practical Steps for Privacy-Conscious Canadian EV Buyers
If you're buying an EV and you care about data privacy, here's what you can actually do about it — regardless of brand.
Read the privacy policy. Seriously. I know no one does this. Do it anyway for your car. Key things to look for: what data is collected, who it's shared with, where it's stored, and what your rights are. Look for the word "sell" — if the manufacturer can sell your data to third parties, that matters for your insurance rates.
Opt out of optional data sharing. Almost every connected EV has settings that control data collection for features beyond basic vehicle operation. Remote diagnostics, usage statistics sharing for product improvement, third-party data sharing — these are often opt-in by default. Opt out.
Understand what "turning off data collection" actually does. You can often limit what's collected, but you typically cannot turn off all telemetry while maintaining connected features like remote app access, OTA updates, and roadside assistance. If you want truly minimal data collection, some of these features need to go.
Consider the whole connected device picture. Your smartphone is almost certainly a more significant data collection vector than your car. If you're concerned about Chinese government access to your data, your first call should be to review what apps on your phone have location access, microphone access, and contact access. The marginal risk of a BYD versus your existing connected device footprint may be smaller than you expect.
For higher-risk individuals. If you're a government official, military personnel, law enforcement officer, or work in critical infrastructure — take the national security concerns more seriously than the average consumer. The aggregate data risk from a connected Chinese EV is genuinely different for someone whose movements and daily routine have intelligence value.
Follow software updates. Automotive cybersecurity vulnerabilities are real. Every connected car has an attack surface. The brands that provide regular OTA security patches are meaningfully safer than brands that don't. Tesla has the best track record on update frequency. BYD's update cadence for international markets is developing; early data is positive.
Buy from brands with documented security audits. Ask your dealer whether the manufacturer has had independent third-party security audits. For BYD, the TÜV review is relevant. For Tesla, Keen Security Lab has done extensive independent research (and found real vulnerabilities that Tesla subsequently patched).
The Insurance Data Question Nobody's Asking
There's a data privacy risk for Canadian EV buyers that gets almost no coverage relative to the Chinese EV discussion, and it's the risk that's most likely to actually affect you personally.
Your driving data is almost certainly being shared with insurance companies.
The 2023 GM OnStar scandal was the most prominent example, but it's not an outlier. Connected car data — braking patterns, acceleration, speed, location history — is commercially valuable to insurance companies. It allows them to price individual risk with previously impossible granularity. For insurers, this is the holy grail: moving from demographic-based pricing to individual behaviour-based pricing.
LexisNexis, which was one of the companies receiving GM driving data, operates a "Risk Solutions" product that aggregates connected car data from multiple manufacturers to create comprehensive driver risk profiles. This data is sold to insurance companies.
How many brands participate in LexisNexis's program? The answer is not fully public, and disclosure requirements are weak enough that you often can't find out by reading the privacy policy. You would need to request your data from LexisNexis directly to see what they have on you.
Verisk operates a similar product called DriveAbility.
The data flows here — from your car to insurance company risk models — are far better documented than any BYD-to-Beijing hypothetical. They're happening right now, to Canadian EV owners, through Western brands. The harm is concrete: higher insurance premiums, insurance denial, and risk scoring that you have limited ability to see, challenge, or opt out of.
If you drive a Tesla and your rates went up, there's a non-trivial chance your driving data contributed to that. If you drive an Equinox EV, same thing.
This is a bigger immediate practical risk for most Canadians than any national security concern about Chinese EVs. But it gets a fraction of the media attention because it doesn't have geopolitical texture — it's just insurance companies exploiting data, which is less newsworthy than China.
How This Compares to Your Smartphone
Your smartphone:
- Contains your location history with precision and continuity far exceeding your car
- Has access to your messages, email, photos, contacts, calendar, and financial apps
- Contains persistent ambient microphone access (if you've granted it to apps)
- Has far more sophisticated behavioral profiling than any car infotainment system
- In many cases runs apps from Chinese developers (TikTok being the most prominent political example) that transmit data to Chinese servers
- Is almost certainly connected to both US and Chinese-owned cloud infrastructure
Your car:
- Records location history and driving behaviour
- May sync phone contacts and calendar data (if you allow it)
- May have camera functionality
- Generates vehicle health telemetry
The car is a serious data collection device. The phone is a more serious one. If you're worried about Chinese government access to your personal data and you have TikTok on your phone, deleting TikTok is a higher-leverage privacy action than refusing to buy a BYD.
This is not an argument to be unconcerned about connected cars. It's an argument that the level of public concern about Chinese EVs specifically is wildly disproportionate to where it sits in the broader personal data risk picture.
The Trade Policy Dimension
We can't talk about this topic honestly without acknowledging that the cybersecurity and privacy concerns about Chinese EVs are being amplified by trade policy interests.
The 100% tariff Canada imposed in October 2024 — the same tariff the US maintains — was explicitly modeled on the justification that Chinese EVs are unfairly subsidized. The security and privacy concerns became part of the rhetorical justification for that trade protection measure.
I'm not saying the security concerns are invented. I'm saying they're selectively amplified when they serve trade protection arguments, and selectively ignored when they would apply to Western brands doing the same things.
The January 2026 tariff deal that reduced Canada's rate to 6.1% was driven by canola exports and political trade relationships. It was not driven by a finding that Chinese EV cybersecurity risks were lower than previously assessed. The risk level didn't change. The trade calculus changed.
This is normal politics. But it should inform how you weigh the cybersecurity arguments you're hearing. When a politician says "Chinese EVs are a cybersecurity risk," they may believe it — but they're also operating in a context where that argument serves trade policy goals. That doesn't make it false, but it means you should seek independent technical assessment rather than taking the political framing at face value.
The independent technical assessment, from what I've been able to find, says: the risks are real, structural, and specific to Chinese legal jurisdiction obligations — and comparable or greater risks exist from Western connected car data practices that aren't receiving equivalent scrutiny.
The Bottom Line for Canadian Buyers in 2026
Here is my honest assessment after everything I've read and researched:
The Chinese EV cybersecurity concern is real but overstated relative to the actual documented risk from Western brands. The structural legal risk from China's National Intelligence Law is genuine and distinct — Chinese companies legally cannot refuse state intelligence requests. But there are zero documented cases of Chinese EV manufacturers providing Canadian customer data to PRC intelligence services, while there are multiple documented cases of Western EV manufacturers mishandling customer data in ways that caused concrete harm.
The regulatory gap is the real problem. Canada has no vehicle-specific data standard, inadequate privacy enforcement mechanisms, and a privacy law written before the connected car existed. This means all EV buyers — regardless of brand — have weaker protections than they should. Fixing that gap matters more than restricting any particular brand.
If you're a regular Canadian consumer, the practical risk difference between a Chinese EV and a Western one is smaller than the political discourse suggests. Your driving data is being monetized either way. The legal architecture for PRC intelligence access exists for Chinese brands; the legal architecture for US surveillance access exists for US brands. Neither is clean.
If you have specific security sensitivities — government, military, critical infrastructure, law enforcement — take the Chinese EV concerns more seriously, particularly regarding proximity to sensitive facilities. This is a niche consideration that doesn't apply to most buyers, but it applies to some.
The right move for privacy-conscious buyers: Regardless of which brand you choose, opt out of optional data sharing, read the privacy policy with specific attention to third-party data sales, disable features that require unnecessary data collection, and request your data from LexisNexis and Verisk to see what's already in your insurance risk profile.
The EV you should be most worried about from a data privacy standpoint is the one you're actually driving today — whatever brand it is — because almost none of them have been designed with meaningful user control over data collection. That's the problem worth solving.

Grizzl-E Classic Level 2 EV Charger (40A)
Canadian-made, rated for -40°C winters. 40A / 9.6 kW, NEMA 14-50. Indoor/outdoor rated, 24-ft cable. The charger built for Canadian weather.
We may earn a commission at no extra cost to you.
Frequently Asked Questions
Are Chinese EVs actually collecting and sending data to the Chinese government? ▼
Is Tesla safer than BYD from a data privacy standpoint? ▼
What does Canada's PIPEDA say about connected car data? ▼
Should I avoid buying a Chinese EV near a military base or government facility? ▼
How can I reduce the data the EV sends, regardless of brand? ▼
What was the Volkswagen data breach and why does it matter for this discussion? ▼
Does BYD's data stay in Canada once it's here? ▼
Why does Canada have a 6.1% tariff now instead of 100%? ▼
Related Reading
- BYD Is Coming to Canada — What the Tariff Deal Really Means for Buyers — The full picture on the tariff deal, what models are coming, and what they'll cost
- Are New EVs Safe? Complete Safety Analysis 2026 — Euro NCAP crash data, battery safety, and winter performance for Chinese EV brands
- BYD Seal Review: $45K Gets You This? — In-depth review of BYD's flagship sedan, now available in Canada
- Best Level 2 EV Chargers for Canadian Homes 2026 — Home charging options that work with any EV brand
- Canada EV Rebate EVAP 2026 Guide — Which vehicles qualify for the $5,000 federal rebate

Read, Plan, Then Charge
Explore our expert articles to understand incentives and ownership costs, use the map to pressure-test charging reality, then grab the Canadian EV Guide for every detail in one place.
Continue Reading
Affordable EV Options in Canada: What Actually Stands Out Right Now

Alberta EV Rebates 2026: What the Province Actually Offers (and What It Doesn't)

